Internal Infrastructure
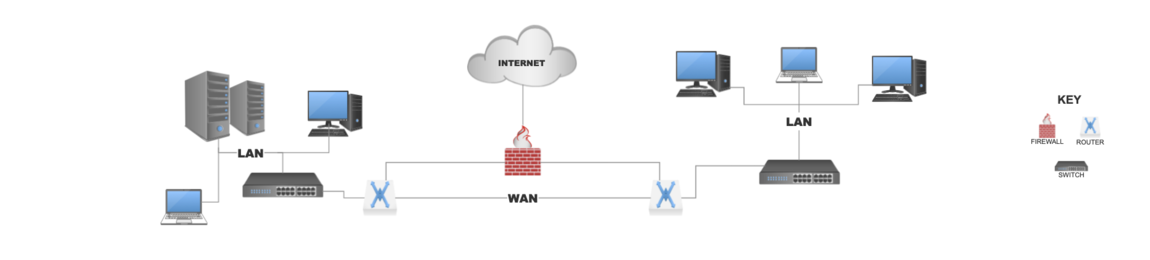
Your internal infrastructure is analogous to the heart and veins of your network. Your physical devices such as switches routers firewalls and servers, supplying the structure to support the blood flow of the system, your data. This system is made up of various networks described as either a LAN, a local area network, or a WAN, a wide area network. Local area networks (LAN) generally span a relatively small area. Maybe a building or a room in a building, allowing servers, workstations, printers, and people to share resources. Wide area networks (WAN) generally span geographical areas such as towns, cities, or even countries in some instances. Connecting various LAN networks to one another. In between these various networks you could have switches, routers, and firewalls. Switches being the aggregator of the systems on the network (servers, printers, workstations), connecting them to one another. Routers are tasked with directing connections over the WANs or LANs, dictating the most efficient route to take to any given resource. The firewall is a sort of gatekeeper if you will, sitting between the networks, allowing or denying access to resources across these networks.
INFOSECURITY, https://tinyurl.com/Equifax-WannaCry
Internal Infrastructure assessments look to identify security concerns within this system. Weaknesses could lie in any given part of this system from the workstations to printers, to switches and firewalls, and anything in between. The weakness could very well be a well-known vulnerability, that with some attention could be resolved quite simply.
Laneden works closely with our clients to understand their drivers and build an appropriate scope of works. Providing a thorough and independent examination of your corporate infrastructure to identify security vulnerabilities within the software, systems, and network configurations. We provide an on-site debriefing of the findings explaining how attackers could potentially gain control of your systems and exfiltrate data. A comprehensive report is written containing an executive summary which gets right to the point of the associated risks identified and is consumable by anyone in the organisation regardless of their technical background. Along with enough detail to allow you to not only understand the potential attack vectors but also concise and clear guidance on how to either mitigate or remediate the concerns.
It’s important for organizations to focus on building a program instead of deploying a tool.
Vulnerability management has to include asset discovery, prioritization and remediation workflows in order to be effective at reducing risk."
TRIPWIRE, https://tinyurl.com/unpatched-vulnerabilities-brea



